Data security is a complex and often hard-to-grasp topic — unless you’re an IT professional who regularly deals with data and cybersecurity problems.
If that doesn’t describe you (and it probably doesn’t), it’s still important to understand data security so that you can ensure your sensitive data is properly safeguarded. After all, data is integral to business success, so data security must be a top priority.
But what exactly is data security? To summarize, it’s the collection of digital privacy measures, policies, processes, and strategies necessary to prevent unauthorized access and use of devices and media that contain or transmit data.
There’s a lot more to data security than a simple summary can convey. This five-chapter guide will help you understand concepts and actionable steps related to data security. Below is a synopsis of what this guide covers. Hopefully the many insights we’ve put together with the help of data security and privacy experts will help you better understand data security and keep your data safe.
Chapter synopsis
- Introduction
- Why is data security important? The answer — which includes information about data breaches, laws, and standards — also provides some context for the chapters that follow.
- Data security threats. Threats to data security come in many forms, including viruses and other malware. Learn about the different ways bad actors can gain unauthorized access to your data.
- Data security best practices. With the help of knowledgeable experts in data security and privacy, we put together best practices you can follow to improve data security in your organization.
- Data security solutions. What solutions can you implement to improve your organization’s data security? Find out in this chapter.
- Form security solutions. Forms are an important tool for carrying out essential business tasks like ordering products, collecting payments, and performing market research. Learn how to make sure the forms you use are secure.
Remember to bookmark this guide for later reference. Data security is a complex subject, and you’ll no doubt need a reminder about terms and next steps to take in your security journey.
Why is data security important?
If you care about the reputation of your company, the security of your intellectual property, and the financial welfare of your customers, then you’re in a position to understand the importance of data security. Without properly safeguarding your data — whether in huge data centers or on mobile devices — the unthinkable can happen: Your trade secrets get leaked to your competitors, your customers’ identities are stolen, and people lose trust in your business.
“In this digital age, data is like gold to businesses — it’s extremely valuable. Remaining successful and competitive requires securing that data and overcoming the challenges associated with that responsibility,” says Jamal Ahmed, privacy and GDPR consultant at Kazient Privacy Experts.
Data breaches
Evan Francen, cofounder and CEO of FRSecure, reiterates the importance of data security when talking about data breaches. There’s always someone who suffers when companies fail to protect confidentiality, integrity, and/or data availability. “Data security isn’t about data or security as much as it is about people. If no one suffered from a breach, nobody would care.”
What is a data breach? Here’s how Francen breaks down the term:
A data breach is a confirmed, unauthorized disclosure or alteration of data. The potential consequences are almost endless, depending upon the data and/or circumstances: identity theft, financial fraud, intellectual property theft, and holding data for ransom, among others. According to some estimates, global cybercrime costs world economies more than $1 trillion annually.
Data security threats
Threats to data security come in many forms, especially as bad actors continue to find new ways of breaking into seemingly secure networks and data stores. And with the increasing reliance on cloud technology, it’s important to ensure systems are up to snuff.
For example, there are a lot of ways data can be transferred from account to account in the cloud. Kevin Hyde, president and cofounder of Layer 8 Security, says if the infrastructure and digital connections aren’t properly secured and configured, your network could have security holes. You might not comply with laws and standards like HIPAA and GDPR. “To ensure you cover your bases and have the right controls in place, you should be using a certified data center,” Hyde says.
Bad actors are constantly looking for weaknesses that will allow them to infiltrate an organization’s network. Below are several of the most common ways they exploit those weaknesses; being aware of them will help inform your data security efforts.
7 network security threats
The types of computer viruses vary, but they all have something in common: They are threats to network security and are detrimental to your organization’s data security. Some viruses or malware (malicious software) open the door for malicious pieces of code, while others focus on corruption and destruction.
Spyware
Spyware is a broad category of malicious software that’s installed on a computer or mobile device without the end user’s knowledge (which is what makes it spyware). The term can refer to many different types of viruses. Some examples of spyware are Trojans, adware, and keystroke loggers.
Trojan horses
What is a Trojan horse virus? Like the Greek story it’s named after, a Trojan horse is a computer program that appears harmless but actually has nefarious intentions.
“Trojans often mask their entrance into a network by posing as simple executable files — think PDFs, Excel spreadsheets, Word documents, and even internet browser plug-ins,” explains Hyde. Unsuspecting employees then download and open these files, providing an opening for malware hidden inside the Trojans to wreak havoc on the user’s computer and the network it’s connected to.
Adware
Adware refers to software that displays advertising through popup windows or sidebars while a program or app is running.
Unlike spyware, adware is not necessarily malicious. In some cases, adware is used to help recover development costs, such as the spend on developing a free game.
Adware examples include in-app ads shown on mobile games and banner ads shown on social media sites. Adware that tracks users’ personal information or browsing habits without the users’ consent can be classified as spyware.
Computer worms
What is a computer worm? It’s malware that replicates itself within a computer’s automated, hidden system files, typically with the intention of opening a backdoor for remotely controlling the computer.
Detecting worms is difficult, and most users don’t suspect their computer has been infected unless the replication consumes too many system resources and negatively impacts functionality. Worms duplicate to spread to other computers while remaining on the originally infected machine.
Rootkits
A rootkit is a program or collection of software tools that enables bad actors to remotely access or control a computing system. Not all rootkits are malicious in nature. For example, rootkits are used to provide remote end-user support (think of a Help Desk). However, rootkits are dangerous because they provide a backdoor for bad actors to deliver malware to the system and can even prevent detection of malware by antivirus software.
DDoS
What is DDoS? DDoS stands for distributed denial of service. In a DDoS attack, multiple compromised systems attack a network resource, such as a website or server, and make it extremely difficult or impossible for legitimate users to access that resource.
Bad actors often exploit a vulnerability in one computer, take control of it, and then do the same to other networked computers. The bad actors then use the collection of hijacked computers in a DDoS attack. For example, an e-commerce company might employ a DDoS attack to crash a competitor’s website.
Phishing
What is phishing? In short, phishing is digital fraud. When a bad actor performs a phishing attack, they pose as a reputable individual or business in an email or other communication medium and distribute malicious links or attachments.
Phishing is much easier than hacking. “It’s much easier and faster to trick people through social engineering than it is to break into a system,” explains Hyde.
Defending against threats to data security
Hyde notes that organizations can take steps to defend themselves against the above network security threats. You can start by understanding there’s no “magic bullet” that can keep your organization secure. “You need to take a layered defense approach since you can never be 100 percent sure where your defenses will fail. It could be your cloud settings, one of your employees, or something you haven’t even considered.”
Here are a few of Hyde’s recommendations for data security:
- Use a spam filter. Since a lot of malware makes its way into the organization through emails and attachments, spam filters can mitigate this risk by stopping the emails altogether — or at least stripping out any attachments that are deemed unsafe.
- Employ a firewall. A firewall forms a digital barrier between your network and the wild west that is the internet. Set security rules to help control ingoing and outgoing traffic.
- Implement a SIEM system. A security information and event management (SIEM) system aggregates data from multiple sources to identify and take action on deviations from normal system behavior. This type of system typically integrates with other enterprise security tools to more cohesively improve data security.
While these network security threats may leave you concerned about your data security, the next chapter will give you great tips on creating a more secure work environment to protect against more than just viruses.
Data compliance regulations
HIPAA
Short for the Health Insurance Portability and Accountability Act, HIPAA was passed by the U.S. legislature in 1996. It applies to all healthcare entities, including hospitals, care providers, health insurance companies, and so on. It also encompasses third-party organizations that do business with these healthcare entities.
HIPAA consists of three rules, as defined by the U.S. Department of Health & Human Services:
- The Privacy Rule ensures that individuals’ health information is properly protected while it’s used to provide and promote high-quality healthcare.
- The Security Rule protects individuals’ health information and allows covered entities to adopt new technologies to improve the quality and efficiency of patient care.
- The Breach Notification Rule forces HIPAA-covered entities to notify affected individuals, the government, and, in certain circumstances, the media, following a breach of unsecured, protected health information.
Francen notes that, while it’s made great strides, HIPAA hasn’t impacted data security as much as some hoped. “Healthcare entities take compliance seriously, but enforcement throughout the industry has been spotty at best.”
GDPR
The European Union (EU) passed the General Data Protection Regulation (GDPR) in April 2016, and it went into full effect in May 2018. Ahmed says that GDPR is the most overarching law around the globe because it’s applicable to EU citizens and any company that processes data associated with EU citizens. The EU has already initiated numerous enforcement actions, which shows the industry that the EU is taking compliance seriously.
Organizations across the globe have also taken GDPR compliance seriously, spending millions to achieve and maintain compliance. This isn’t surprising given how large noncompliance fines can be: anywhere from 2 percent of the worldwide annual revenue of the prior financial year on the lower level to 4 percent on the upper level, depending on the infringements. This could amount to tens of millions of Euros. “GDPR might be the most impactful data privacy law in history,” says Francen.
Privacy Shield Framework
The Privacy Shield Framework (PSF) is a safeguarding mechanism maintained by the U.S. Department of Commerce. Its purpose is to facilitate commerce and data transfer between U.S. and European countries in a way that’s consistent with EU law.
European countries aren’t permitted to transfer data to the U.S. or any other country that has less stringent data privacy laws than the EU. “The framework is voluntary and facilitates GDPR compliance, but it doesn’t substitute for GDPR compliance,” explains Francen.
Companies can self-certify their compliance with certain principles to join the PSF. To note, both Ahmed and Francen indicate that the PSF supersedes Safe Harbor and its certification.
PCI DSS certification
The Payment Card Industry Data Security Standard (PCI DSS) is a set of security requirements established by the main industry players — VISA, Mastercard, Discover, etc. — to protect payment card data security. This industry standard was originally developed to stem legislative action. “It has significantly improved the security of payment card data,” says Francen.
He notes there are four levels of compliance, which are based on how an organization collects, stores, creates, and/or transmits payment card data and in what quantity. “Generally, more data — and more interaction with that data — equates to more scrutiny.”
Now that you have an idea of the importance of data security, let’s move on to the top data security threats facing organizations like yours.
Data security best practices
Securing your organization’s data can be like climbing a mountain, especially if you’re not sure what to do or what advice to follow. To make your climb easier, we’ve gathered some data security best practices for specific areas of concern below. (For a more general list of data security best practices, check out this post.)
Data security policy: 4 best practices to follow
Workforce
“The human element of data security is always the most vulnerable,” says Ahmed. Even with the best security policies and procedures in place, people can often circumvent your plans — whether intentionally or accidentally.
For example, an employee may forget to remove personal information before sending it to a third party, mistakenly leave a laptop unattended, or neglect to encrypt devices like USBs or mobile phones. All of these actions represent weak points in data security, which is why data security training is so important.
Training your workforce on proper data security protocols is necessary to safeguard your data. Ahmed says you can deliver training modularly through digital means, bring in an onsite trainer, send monthly newsletters, perform simulations, or do some combination of these methods.
“The important thing is that you deliver training in some form continuously. Data security training should be an ongoing effort,” Ahmed says.
Training is particularly important in the healthcare industry. Medical facilities like clinics and hospitals collect sensitive information and medical histories. If bad actors stole this information, patients could face financial harm such as long-term credit issues and insurance complications due to their medical data being used fraudulently. To help guard against this risk, follow these steps.
Francen emphasizes the importance of instilling a culture of data security in the workplace and helping employees to internalize it. He says that people are naturally creatures of habit, and nothing motivates them more than their own personal matters. With this in mind, companies should focus on helping employees develop good security habits at home, where security has a more direct impact.
“If people learn good security habits at home — where they’re protecting themselves and their families — those same habits will translate into better security habits at work,” Francen says.
Identity and access management
Identity and access management (IAM) is a role-based framework that manages digital identities. The purpose of IAM is to control user access to important or sensitive information.
According to Ahmed, IAM is an important risk mitigator: Limiting access by user identity limits the likelihood of users getting their hands on something they shouldn’t be able to see in the first place. “In addition, if a breach should occur, IAM can help you quickly identify who was involved with user access logs,” Ahmed says.
He adds that effective IAM requires assessing each user and their job role individually, then creating a tailored access profile: What does each user need to access in order to perform their duties?
Francen notes that companies often fail at managing IAM because they try to tackle multiple areas — identification, authentication, authorization, and accounting — all at once. “Master identity management first before attempting to master the other areas.”
Network security monitoring
With network security monitoring (NSM), a system — or hybrid system and service provider — continuously monitors your network for security threats, vulnerabilities, and abnormal behavior. NSM can be simple or complex and cover a range of areas, from access control and antivirus to intrusion prevention and behavior analytics.
Francen says that normal network traffic looks one way, while threat traffic looks anomalous in some respect. Identifying threats and/or data leakage early can mitigate financial and reputational damage to the company. “But the keyword here is early,” Francen says. “Threats don’t always manifest themselves at the time of compromise. Oftentimes, there’s a threat pattern that tips off a security professional to an impending compromise.”
Data backup
Ahmed recalls the old adage, “Don’t put all your eggs in one basket.” It’s the perfect saying for data backup because not backing up your data puts your company at risk of losing important data.
“Data is a valuable commodity, so performing regular and consistent data backups will minimize data loss and operational downtime,” Ahmed says. “You can restore your lost data and get back up and running much quicker.”
Francen provides steps you can take to determine your best path forward with data backups:
- Get management approval before starting.
- Identify system and data owners.
- Conduct a business impact analysis.
- Use the recovery point objective (RPO) and recovery time objective (RTO) to determine
- The technology you need to use
- How often you should back up the data
- What type of backup you’ll use (full, incremental, differential, etc.)
- Where backup data will be stored
- How backup data will be transferred to storage
- Document the backup strategy in a way that an outsider would understand.
- For every repeatable process, document a procedure.
- Define test and review schedules.
- Get final approvals.
With these best practices out of the way, next we’ll move into useful data security solutions you can employ.
Data security solutions
There are countless tools and methods for securing your data, ranging from simple key fobs to complex data scrambling techniques. Each has its place, but which ones you implement will depend on the sensitivity of your data and the level of rigor you want to establish within your organization.
Below are several key data security solutions you should consider adding to your arsenal.
Data security solutions to implement
Encryption key management
Encryption key management (EKM) is the collection of policies and processes that help protect, store, organize, and back up encryption keys — access mechanisms that safeguard data by scrambling and unscrambling it for authorized users.
“The point of EKM is to ensure no one sees your information, except for those who are supposed to see it, by keeping the keys used to decrypt your data separate and secure,” says Russo. For an example of what encryption looks like, he tells people to check their browser for the padlock symbol in the navigation bar. That lock indicates there’s an encrypted connection between the web server and your browser.
Russo says that EKM is important for securing sensitive data — even more so for industries like healthcare, where companies need to comply with strict HIPAA regulations. If a laptop is stolen, for example, encryption could save the day: “If properly encrypted, a laptop would be fully protected. The thief could make off with it and still not be able to read it. The laptop and the data stored on it would basically be useless unless the thief has the private keys used to scramble the data. Utilizing proper EKM would prevent that scenario.”
We answer several FAQs about EKM in this post, including the challenges organizations face regarding this practice and how bad actors might circumvent your encryption efforts.
Data classification
Data classification involves organizing data into specific categories for greater effectiveness and efficiency, making it easier to find and use. The classification scheme you devise should be simple enough for all employees to abide by with ease; otherwise, you run the risk of employees misclassifying data, which limits the effectiveness of the process and makes data less (or more) secure than it needs to be.
Classification schemes differ from company to company. Some consist of five categories, with higher categories containing more sensitive data. The first category might be everyday information that anyone can access, such as price lists. Data in the fifth category might be highly confidential and present financial risk, such as employee social security numbers or customer credit card numbers.
Cloud data security
Cloud data security involves the technologies and policies designed to protect information, applications, and infrastructure associated with cloud computing and storage.
Tim Russo, president of Wireguided, says that unsecured cloud data is vulnerable to bad actors like hackers. He notes that many companies assume any data in the cloud is automatically secure and don’t take the necessary steps to ensure that security.
“A problem can occur when sharing data with third parties,” Russo says. “A few cases have been made public where these entities left other companies’ private information wide open for anyone to access on the internet — sometimes for years. Organizations need to employ additional security measures when utilizing the cloud, such as multifactor authentication.”
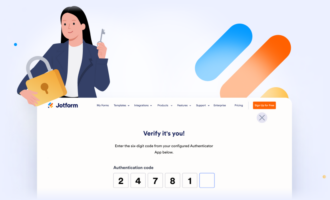
Strong customer authentication
Two-factor authentication has graduated to strong customer authentication (SCA) and now includes additional authentication methods. SCA is based on using at least two of three verification elements:
- Knowledge: something only the user knows, like a password or pin number
- Possession: something only the user possesses, such as a debit or credit card, a key fob or token, or a text (if the user has a mobile phone)
- Inherence: something the user is, which typically involves a biometric identifier like facial or voice recognition, a fingerprint scan, or even behavioral biometrics like speech patterns
Generally, the more sensitive the data is, the harder it should be to access. That means employing an additional verification element or a more complex option within a verification element — such as using speech patterns instead of simply a voice.
Tokenization
As a process, tokenization replaces sensitive data with unique symbols that retain all the essential information about the data without compromising its security.
This process helps secure information in transit and at rest, and can help comply with regulations like PCI DSS, HIPAA, and GDPR. Unlike encryption, which this process is often compared to, tokenized data never leaves the organization.
Tokenization is often used with point-of-sale systems to convert credit card numbers into randomly generated values, or tokens. That token is only relevant to a specific context, such as an individual transaction with a particular merchant. If a hacker does manage to steal the data, tokenization ensures the bad actor cannot identify actual card numbers.
Other examples of tokenization usage include bank transactions, vehicle driver information, and any context where randomizing values can help conceal or obscure identifying information.
Data masking
Data masking creates fictitious — but seemingly authentic — data that can be used for things like software testing and user training. This tactic protects the real data but gives developers and other IT personnel meaningful data points to work with as needed. Note that the format of the data doesn’t change, though the values do.
Data masking is useful, but it’s not necessarily a highly secure practice. Ahmed says that masked data can often be cracked if you have the right information. “As long as it’s relevant to the data, one piece of information can unlock all your masked data. For example, all a bad actor might need is a date of birth or zip code.”
Next up, we dive into a specific tool businesses use to collect data (and that must be protected): forms.
Form security solutions
At some point, almost every organization needs to use a form. Forms are a critical component of a number of business activities, including:
- Customer product ordering
- Online payments
- Data collection for market research
- Customer contact
- Employee satisfaction surveys
- Customer feedback
The list is endless. But if you use forms, you need to protect the information you collect with them — much of which is sensitive. Jotform is an easy-to-use, secure form builder — which means you’ll never have to worry about whether your data is safe.
Jotform and data security
Jotform uses Hypertext Transfer Protocol Secure (HTTPS). (Recall the padlock example from Chapter 4.) This protocol ensures that any data transferred between a user’s web browser and a website is secured through SSL — an encryption technique that prevents bad actors from reading or using data, even if they are able to extract it during transit.
So when users access your form and fill in the requested details, you (and your users!) can rest assured that data is secure while in transit between your browser and Jotform’s servers.
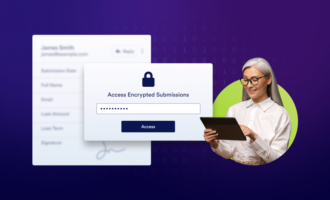
Form data encryption
Beyond the standard HTTPS usage that provides you with secure forms, you can also encrypt your forms. With encrypted forms, sensitive data is also encrypted at rest — not just in transit. Jotform offers many encrypted forms, complete with an encryption key only you have access to. Only the key holder can read encrypted data. (A data privacy expert provides a great metaphor for better understanding the concept of an encryption key in this post.)
This additional layer of security enables Jotform to offer HIPAA-friendly forms — so healthcare organizations can collect and organize medical information, patient feedback, employee applications, and payments in one place.
Mobile data security
Data security doesn’t stop at the desktop. Everyone’s mobile these days, and a smaller screen shouldn’t limit your ability to do business using forms. You need forms that are mobile-friendly and just as secure as their desktop counterparts.
Jotform takes care of that with Jotform Mobile Forms, an app for iOS and Android. Even if you create your form on a web browser, you’ll still be able to view, complete, and edit it with the app. Plus, you can fill out forms offline, so you don’t need to worry when there’s no Wi-Fi available or your mobile data is spotty or limited. Just like with web forms, secure mobile forms come standard, and you can add encryption for extra security.
Data privacy
You must log into your Jotform account to view your submission data. If someone knew the unique, almost impossible-to-guess URL of a single submission, they could view only that particular submission (not all of your submissions). This is incredibly unlikely to happen, but you can add an extra layer of protection to your form by requiring a login to view each submission.
More about your data security guides
Evan Francen
Evan Francen is the cofounder and CEO of FRSecure, an information security consulting company with more than 1,000 clients across the U.S. He’s also the author of Unsecurity: Information security is failing. Breaches are epidemic. How can we fix this broken industry? Prior to starting FRSecure, Francen spent more than 15 years working as an information security professional and corporate leader at private and public companies.
Jamal Ahmed
Jamal Ahmed is the lead privacy and GDPR consultant at Kazient Privacy Experts, a firm that provides EU representative and data protection officer solutions to organizations globally. He is a Certified EU GDPR practitioner, Certified Information Privacy Professional Europe (CIPPE), and Certified Information Privacy Manager (CIPM). Ahmed also has nearly a decade of global experience in data protection and security across financial services, home security, real estate, human resources, and nonprofit sectors.
Kevin Hyde
Kevin Hyde is the president and cofounder of Layer 8 Security, a cybersecurity consulting, advisory, and technical services company that creates risk management solutions for evolving information security and compliance needs.
Tim Russo
Tim Russo is the president of Wireguided, a company that provides managed IT services, cloud solutions, training, and other IT solutions. He has six professional certifications and works with his team at Wireguided to help organizations manage their IT infrastructure.






















Send Comment:
3 Comments:
June 24, 2021
I am based in South Africa and from 1 July the POPI Act will be implemented with more stringent requirements to protect personal information of individuals. Can you provide me with Certificates and protocols that reflect how Jot form complies with international laws in this regard. I also need to know where data is stored that I enter on Jotform (where is the servers located) and whom has access except for me. Thanks George
June 4, 2021
Great post! Thanks for this informative and detailed article. Data is essentially inert and passive, lacking an inherent ability to either control its own fate or mitigate risks while under process. Data loss and theft is a result of the problem. We do not control or govern data. In reality, only users, applications and machines are “controlled.” But you can now make it possible for data to be self-aware, self-protecting, self-acting to reduce the dependency on human behavior and infrastructure.
October 2, 2019
A good scare is worth more to a man than good advice, they say, but you should never underestimate the reasoning behind the advice.
That is really true. As a tech professional who has specialized in data security, I have experienced so much threats, breaches and even big time failures during my career. However, I feel like I cannot warn the people strongly enough of the importance of data security. Because, as the high tech gadgets are around us more than ever, we voluntarily allow the AI to create a replica of ourselves. You don't have to be kidnapped for a particular personal detail about you. If your sensitive data is somehow breached, it's very probable that that detail would be captured as well. So, everyone has to be really careful while subscribing to a newsletter or creating an account on a social media application. Terms and conditions section that you automatically check does actually matter.
Thanks for the insightful article. If I were the author, I would have written the similar stuff, more or less.