Encryption key management is incredibly valuable when it comes to securing your company’s sensitive data. With help from two data privacy experts, we’re going to explain how encryption key management works and the impact it has on data security.
4 FAQs about encryption key management
What is encryption key management?
What challenges are involved with encryption key management?
- Vulnerability: ensuring the security of encryption keys from insider threats (employees) and external parties (hackers)
- Scalability: managing encryption keys effectively as your data grows and you create more keys to keep track of
- Policy: governing data access based on appropriate and practical policies
- Access: making data available to authorized users
- Complexity: supporting multiple encryption standards across numerous applications and databases
How do you make the most of encryption key management?
- Be prepared to handle problems when things go wrong. Have a clear plan and process to follow, and assign owners responsibility for carrying them out. Run regular simulations, making sure each person is aware of their responsibilities and who is responsible for other steps.
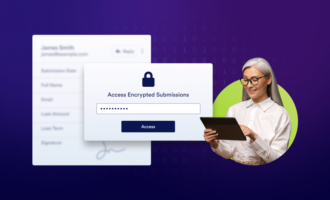
- Restrict access to encryption keys to only those who absolutely need it to perform their duties, regardless of seniority.
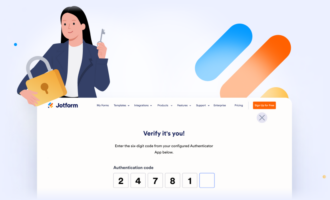
- Only use enterprise EKM services that are proven to meet Federal Information Processing Standard Publication 140-2 (FIPS PUB 140-2).
How might bad actors circumvent or bypass encryption key management?
Encryption key management (EKM) is the collection of policies and processes that help protect, store, organize, and back up encryption keys — access mechanisms that safeguard data by scrambling and unscrambling it for authorized users.
Jamal Ahmed, privacy and GDPR consultant at Kazient Privacy Experts, helps simplify the concept of encryption key management with a metaphor. Imagine you have a house (your company). Inside are multiple rooms (databases, servers, applications). In each room, you store gold (data). Given the importance and value of gold, you’d want to protect it, right?
You’d install a lock (encryption) on your front door to which you have the key (encryption key). For extra protection, you’d also add a lock to each room, meaning you’d have a set of keys — one for the front door and one for each room. The keys grant access to your valuable gold, and the better job you do of protecting those keys (encryption key management), the safer your gold will be.
Ahmed says the operational part of EKM is where most organizations struggle. He separates the challenges into five key areas:
Ahmed says there are three actions organizations can take to make their EKM efforts worthwhile:
Protecting your encryption keys is paramount to safeguarding your data. “If a malicious party gets their hands on your keys, it’s game over,” cautions Ahmed. To avoid this, he says, you can employ dual control, where two or more separate key holders are required to hold the keys. No one person is able to access all of the keys.
Ahmed also recommends separation of duties, meaning the key holder isn’t allowed to handle the data and the person who handles the data isn’t allowed to hold the keys.
Will Ellis, founder of Privacy Australia, also calls out human error as a culprit in compromised keys. He says that someone could use a key for a purpose it was not created for, use it multiple times, not change a key frequently enough, store a key on a sticky note or other unprotected source, or fail to delete a key. “And there’s always the possibility that an employee with access to your keys has malicious intentions, making them a dangerous insider threat.”
Curious about other areas of data security? We created a lengthy guide on the topic to help you ensure your data is as safe as possible.
























Send Comment: