No one wants to be the victim of theft, especially when that theft involves their medical information. The 2017 World Privacy Forum report, The Geography of Medical Identity Theft, noted the following frustrating and potentially costly consequences of medical identity theft:
- Long-term credit issues and financial difficulties, such as being unable to qualify for mortgages, because of debt resulting from the fraudulent use of personal information
- Large bills for products or services that victims did not purchase or receive
- Maximums, restrictions on copays, and other insurance limits due to fraudulent use of medical data
- Inaccurate information becoming part of the victim’s health records (which can lead to difficulty in getting proper healthcare, being denied jobs, and even losing custody of children)
Steps your organization can take against medical identity theft
Often medical information is stolen because of breaches at the organizations that handle healthcare information. Covered entities and business associates must do everything they can to prevent this.
Enhance verification. Andras Cser of Forrester Research suggests that providers improve how they verify a person’s identity by incorporating knowledge-based authentication and ID verification via one of the credit bureaus. Using additional methods to identify someone reduces “reliance on the Social Security number for authentication and identification,” says Cser.
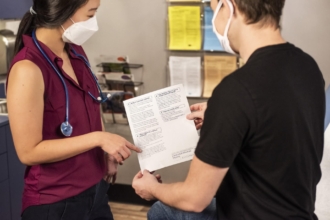
Train your staff. Organizations handling electronic protected health information (ePHI) should focus on their employees just as much as their technology. Generali Global Assistance President Paige Schaffer recommends training staff on ways to mitigate the risks of medical identity theft, including shredding any paperwork that doesn’t need to be retained, only gathering information on a need-to-know basis, protecting both paper and digital records, using digital instead of paper records as often as possible, and looking out for phishing emails.
Train your patients. Heather Lomax of Blaze Systems recommends that patients be knowledgeable about identity theft as well. While training often focuses on internal threats, patients also need some education because of their ability to access online health portals on potentially unsecured computers. When patients know more about these risks and how to defend against them, there is a greater likelihood they won’t use unsecured computers to access their medical data.
Patients should understand that sharing their medical information puts them at risk. There is a good chance their data will be used fraudulently if someone requests it from them by email or over the phone. Patients have to sign an authorization in order to allow the release of their health records over the phone. Your patients should end a phone call immediately if the caller asks for healthcare information and cannot immediately confirm the organization from which they are calling.
Incorporate snail mail. Insurers can use snail mail as a way to confirm treatment with patients.
Safeguard ePHI. Protecting against identity theft is, in large part, about following the parameters of the HIPAA Security Rule: setting up technical, administrative, and physical safeguards to mitigate risks uncovered through routine risk assessments.
Technical protections are certainly a high priority, according to Lomax. You need to have strong systems integrated with security best practices. The portals used by carriers, as with other ePHI systems, should use strong managed multifactor authentication.
You also should have signed business associate agreements (BAAs) in place.
Know how to respond and recover. You need to have an incident response plan that is thorough and routinely updated. The plan should discuss the steps to be taken if a breach is detected, both in terms of stopping the invasion and properly handling any ePHI that is involved. Notifications should be sent to patients, as well as to the HHS and potentially the media (per the Breach Notification Rule).
Choose strong partners. If you think your organization could use outside help with infrastructure setup and management, tap the expertise of credible healthcare service providers who have experience meeting federal rules for a spectrum of organizational types and sizes. A strong partner will be ready and willing to sign a BAA.
Action against medical identity theft
There were approximately 2.3 million cases of medical identity theft in 2014, and that number is growing. Given all the potential consequences of this form of fraud, it is vital to take steps to prevent it by decreasing the risk of a breach. While training is critical, you should also set up proper protections and seek third-party expertise as necessary.




























































































Send Comment: