“The [Digital Signature] Standard specifies a suite of algorithms that can be used to generate a digital signature. Digital signatures are used to detect unauthorized modifications to data and to authenticate the identity of the signatory.” — National Institute of Standards and Technology
Digital signatures and electronic signatures might sound alike, but they’re quite different. Digital signatures are cryptographic “nuts and bolts.” An electronic signature might just be a typed word, ticked box, or recorded voice. A digital signature is technology that uses complex mathematics to encrypt and decrypt data. This behind-the-scenes encryption is what makes electronic signatures work.
Digital signatures use PKI as a way to verify the identity of a signer. PKI uses two keys, one public and one private, for unique identification. Both the sender and recipient have a digital certificate from a certificate authority. These digital certificates work together like a driver’s license or passport and an ID reader.
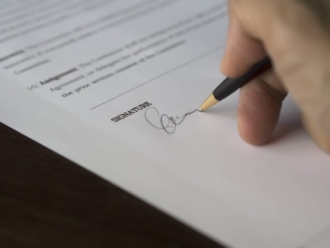
For example, Company One needs Alex to sign a contract renewal. During the process, Alex signs using her private key, which encrypts the contract. Alex also gives Company One her public key. If the public key provided to Company One cannot decrypt Alex’s signature, the digital signature is rejected.
Depending on which digital or electronic signature you’re using, you might need to take extra steps for additional security. For example, you can use two-factor authentication. When triggered, it attempts to authenticate your identity by sending a message to your mobile phone. It makes sure the person signing is you and not someone using your login or key.
You may not always need such a high level of security. For low-risk scenarios, there are simpler security options offered through electronic signature providers. Do low-security options affect the validity of a signature? Not necessarily. For example, an e-signature provider without a digital signature can still identify a valid audit trail. They could get it by examining IP address, time stamps, or browser information.
When choosing an e-signature or digital signature solution, your organization will need to balance the needs of security, time, legality, and cost.
As mentioned previously, both e-signatures and digital signatures are legitimate signatures. According to the ESIGN Act, an electronic signature does not have to be a typed name. What other types of signatures are acceptable?
Just so you know
Collect e-signatures seamlessly from any device with Jotform’s E-signature widget! Add it to your online form to generate signed agreements, consent forms, waivers, and faster.
Other e-signature types
Along with digital signatures and e-signatures, other types of electronic signatures are becoming commonly available.
Click-to-sign. A click-to-sign signature is a situation where a single click of the mouse signs the document.
There are legal conditions to be aware of if you’re using a click-to-sign solution. With click-to-sign signatures, the legal principles of intent, consent, attribution, and association still apply. For example, the signer must intend to click and consent to doing business this way. The signature needs an auditable trail of data that attributes the signature to the individual, and the data must be directly associated with the document.
Before using click-to-sign on your documents, check local laws regarding these signatures. In most of the United States, click-to-sign is legally binding. Across the border in Canada, investment dealers can use e-signatures.
Blockchain. Originally used in cryptocurrencies, blockchain is now finding uses in mainstream industries, such as monitoring supply chains in fashion. The technology is useful for determining the authenticity of transactions using a distributed ledger. Blockchain is great for maintaining accountability, for example, of currencies like Bitcoin. However, it may not be as useful for situations when an individual or organization wishes to be anonymous.
Biometric signatures. Biometric signatures use information about your body to verify authenticity. They add a part of your body that’s unique to you, such as
- Fingerprints. Not just used at a crime scene or an airport anymore, fingerprints are now crucial to consumer technology. Fingerprint scanners are found on smartphones and on credit cards in the United Kingdom. While they provide extra security, they are not as safe as you might think. Researchers have developed “deep master prints” that can hack fingerprint scanners.
- Hand geometry. This method calculates the finger lengths and palm size of users.
- Eye scans. Eye scans analyze the patterns of blood vessels in the retina or colors and lines in the iris. These scans are difficult to fake because the patterns are unique to each person.
- Face ID. Infrared dots shoot out and measure a unique 3D face image. Used in the iPhoneX, Apple claims Face ID is 20 times harder to break than its fingerprint scanner.
- BioSig-ID. This authentication software captures unique movements and gestures as the signer draws a four-character password with a finger, stylus, or mouse.
While biometric signatures are harder to forge, they’re also harder to replace. For example, you can quickly create a new password if someone guesses yours. However, you can’t really come up with a new face if someone hacks your Apple Face ID.
Both complex and simpler types of signatures will continue to have their uses. The type of signature you choose will depend on the reason you need the signature. The level of security and sophistication should match the occasion.
In the next section, we’ll examine some common scenarios when you might need an e-signature.












































































Send Comment: