If you lead IT or systems at a medical practice, you’re used to balancing competing priorities.
On one side, clinical and operational teams are pushing for faster, more flexible tools. They want to move quickly, adapt workflows as needed, and keep up with patient expectations.
On the other side, keeping up with cybersecurity standards and regulations is an ongoing challenge. The expectations around how protected health information (PHI) is handled, audited, and secured continue to rise.
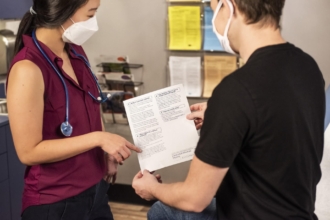
And right in the middle of that tension sits something deceptively simple: patient intake.
Intake isn’t just a form, it’s a risk to PHI protection
At first glance, intake might seem like a lightweight tool. It’s just forms, right?
But in reality, it’s one of the first points where sensitive patient data enters your systems — and one of the least governed in many organizations.
That’s what makes it risky.
Intake has evolved into a critical data management layer that touches PHI, operational workflows, and downstream clinical systems.
And when governance isn’t built in, problems don’t show up immediately. They show up quietly — for example, when
- PHI gets downloaded to desktops or shared via email
- Staff store data in loosely controlled drives or spreadsheets
- Teams create their own workarounds to move information
Each of these actions might solve a short-term need. But over time, they create exposure that’s difficult — if not impossible — to control.
The real challenge: Enabling speed without creating shadow IT
Here’s the reality most IT leaders are facing: If you lock intake down too tightly, teams find ways around restrictions.
If you leave it too open, you introduce serious risk.
That’s the balancing act.
When intake tools lack governance, they create risk. But when they’re overcontrolled, they slow down operations and push teams toward using software without the knowledge or approval of IT — also known as shadow IT.
Shadow IT can lead to
- Duplicate forms across departments
- Inconsistent data structures
- Manual CSV exports and copy-paste workflows
- No clear audit trail for information
From an IT perspective, this isn’t just inefficient, it’s ungovernable.
Why intake has become a governance problem
Intake sits at the intersection of usability and compliance.
The intake process has to be
- Simple enough for patients to complete on their own devices
- Flexible enough for different departments
- Controlled enough to meet HIPAA and internal security standards
When structure is missing, three major risks tend to emerge:
1. PHI exposure becomes inevitable
Data spreads across endpoints, inboxes, and shared drives, increasing the number of access points for cyberattacks.
2. Access control breaks down
Without role-based permissions, organizations drift toward an “everyone can see everything” model, which directly violates the principle of least privilege: that users should, by default, only have access to the information necessary to do their jobs.
3. Integration shortcuts take over
Manual exports and ad hoc workflows replace secure, auditable data pipelines, introducing errors and bypassing controls.
And in today’s cybersecurity environment, these aren’t theoretical concerns. Healthcare continues to be one of the most targeted sectors for cyberattacks.
What “good” intake actually looks like for IT teams
High-performing IT organizations don’t treat intake as a standalone tool.
They treat it like production software.
That shift changes everything.
Instead of ad hoc forms, intake becomes a structured system with these three core layers.
1. Governance (the foundation)
Governance sets the structure for how data is accessed.
- Role-based access ensures staff only see what they need.
- PHI and non-PHI workflows are clearly separated.
- Audit logs track who accessed what and when.
This creates enforceable boundaries without slowing teams down.
2. Workflow orchestration (the engine)
An intake workflow doesn’t just collect data. It triggers actions:
- Submissions route automatically to the right teams.
- Approvals and reviews follow defined logic.
- Exceptions are handled consistently.
- Activity is logged for both operations and security.
No more inbox-driven workflows. No more guesswork.
3. Integration (the connective layer)
Integration with other software is where many intake systems fall apart. But it’s also where the biggest gains happen.
In a well-designed setup,
- Data flows securely into storage systems and electronic health record (EHR) systems via APIs
- Alerts go to monitored channels (not personal inboxes)
- Systems stay in sync without manual handling
This integration-first approach eliminates copy-paste workflows while preserving traceability.
The mindset shift: Governance actually enables speed
It’s a common assumption that governance slows teams down.
In practice, the opposite is true.
When guardrails are clearly defined through data classification, access policies, and integration standards, teams move faster because they’re no longer inventing their own solutions.
Standardization becomes an accelerator.
Instead of building forms from scratch, creating one-off workflows, and constantly asking IT for approvals, teams operate within a system that’s already designed to work.
Why this matters more now than ever
Regulatory expectations aren’t standing still.
Guidance from HHS and the Office for Civil Rights continues to emphasize the need for
- Risk analysis
- Access controls
- Auditability
These aren’t nice-to-haves. They’re foundational to HIPAA compliance.
If your intake system can’t support these functions natively, your team ends up building its own controls, which are often fragile, expensive, and hard to maintain.
Where Jotform fits into your architecture
For IT and systems leaders, the goal isn’t just to digitize intake — it’s to govern it at scale.
Jotform is designed to support that shift.
It brings together the three layers that matter most:
- Governance: Role-based access, team segmentation, centralized control
- Workflow orchestration: Rule-based routing, approvals, and task management
- Integration: APIs, webhooks, and native connectors for secure data flow
Instead of intake being a disconnected entry point, it becomes part of your broader systems architecture: secure, auditable, and scalable by design.
The bottom line for IT leaders
If patient intake still relies on loosely governed tools, manual workflows, or workarounds, it’s not just inefficient.
It’s a growing risk.
But when you treat intake like the system it actually is — something to structure, govern, and integrate — you create a different outcome:
- Stronger PHI protection
- Clear access boundaries
- Fully auditable workflows
- Faster, more consistent operations
And most importantly, you eliminate the constant tradeoff between speed and control.
Because with the right foundation in place, you don’t have to choose between them anymore.
—
Watch “Intake as infrastructure: A strategic framework for medical operations leaders” webinar.





























































































Send Comment: