In 1996, the U.S. Congress passed the Health Insurance Portability and Accountability Act (HIPAA) to protect personally identifiable patient health information (PHI). Subsequent amendments, including the Privacy Rule in 2002 and the Security Rule in 2003, further reinforced laws for all healthcare organizations and any business associate or third party responsible for handling electronic protected health information (PHI), or ePHI.
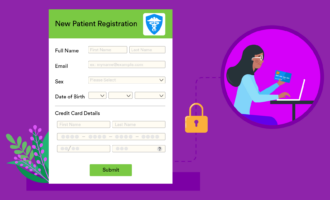
The data held by healthcare practices, hospitals, and other medical facilities is often very sensitive. In the wrong hands, it could be very damaging. For example, if a fraudster knew someone’s name, address, and social security number, they could wreak all kinds of havoc.
Reporting requirements
A unique feature of HIPAA is the requirement that healthcare organizations report data breaches and violations to the Office of Civil Rights (OCR), which enforces HIPAA regulations.
There are specific guidelines for notifying the individuals affected by a data breach. In a major breach, the healthcare organization must report the breach directly to the patients affected and release details of the breach to the media.
The OCR also maintains a list of all reported data breaches, candidly known as the wall of shame breach report.
Reported insider jobs
It’s estimated that over half of all data breach incidents in healthcare organizations are the result of an inside job. This may be a result of employee negligence, human error, or malicious intentions.
A primary cause of data breaches is unprotected administrative credentials and shared usernames and passwords. Lost and stolen devices as well as weak network security are also major contributing factors.
According to a study conducted by Carnegie Mellon University about the threat of insider data breaches in healthcare from 1996 to the present
- 67 unique insider cases aimed to defraud a healthcare organization
- 12 cases resulted in the theft of intellectual property
- Nine cases involved sabotage
- In all cases, financial gain was the primary motive
Malicious actors can sell compromised information to criminals who use a victim’s identity to fraudulently access medical care.
How to defend against insider threats
The insider threat is one of the most challenging dangers to HIPAA compliance. It may not be possible to completely eliminate the risk rogue employees pose. In addition, not all incidents are malicious; in fact, many of the breaches posted to the OCR site indicate that employee negligence was a primary factor.
A total of 71 percent of cybersecurity incidents related to healthcare data involve employees. This is the only industry in which employees and internal vendors pose the biggest cybersecurity threat to organizations. What can be done to defend against these threats?
The following can greatly limit your healthcare organization’s exposure to these dangers:
- Choose the right business associate. Choosing a security-oriented business associate, such as a third-party courier or managed service provider, can dramatically increase ePHI security. The business’s security best practices, administration, and physical and technical safeguards must align with HIPAA. The organization must also sign a business associate agreement.
- Know exactly where your HIPAA data is located. It’s critical for healthcare practices, business associates, and service providers to know exactly what ePHI is retained digitally and which systems process, transmit, and save it. Understanding how ePHI travels through the organization can help you bolster security and ensure compliance.
- Institute robust access controls. One of the best methods of protecting any system is to enforce a stringent username, password, and authentication security practice. This ranges from strict password controls, user account expiration dates, enforced password changes, a strong password policy, file system permissions, and application authentication. When handling ePHI, multifactor authentication — such as a mobile phone key exchange, key fobs, and fingerprint scanning — must be used.
- Develop a strong mobile phone policy. It’s critical to control mobile phones used for business. Mobile devices have access to a plethora of ePHI. Emails, scans, test results, x-rays — the list goes on. Security controls for mobile devices can control user privileges, ensuring only approved mobile applications are used (such as in-house email clients).
- Use tight endpoint control measures. Any business devices used in healthcare, such as laptops, tablets, and medical equipment, must properly secure ePHI, both during transmission and storage. If an endpoint device is lost, you should be able to delete the data with remote wipe technology.
- Automated compliance and vulnerability assessment. You must conduct risk assessment testing to ensure safeguards and technology are working correctly. You can do this through external penetration testing on infrastructure and endpoints, as well as by interviewing personnel.
- Educate employees. Staff training, learning initiatives, and regular technology updates help employees foster a secure work environment. Some personnel might not think twice about sharing credentials; however, educating them about best practices can eradicate many bad habits and significantly bolster ePHI security.
- Always have a backup. Backup and disaster recovery capabilities are essential. If an insider is capable of sabotaging critical computer systems, the ability to restore ePHI from a backup becomes paramount. If sabotage causes a system outage, disaster recovery and business continuity processes must be in place to restore system access as soon as possible.
Insiders will always pose some level of threat when it comes to data breaches, whether intentional or not. However, with the correct safeguards in place and robust checks and balances, it’s possible to diminish this risk significantly.



























































































Send Comment: