It’s an unfortunate reality that personal health data, such as medical records, is a high prize for hackers and identity thieves. In fact, between 2009 and 2019, there were more than 3,000 breaches of medical data involving 500-plus records in each breach. Those records contain highly sensitive personal and protected health information (PHI). Healthcare providers, hospitals, and medical clinics are prime targets in a world beset by cyberattacks.
One way to keep that PHI secure is to ensure that your medical organization has a firewall in place and that it’s configured correctly. A study revealed that 76 percent of organizations that experienced a data breach had a firewall that wasn’t set up correctly. And it’s not enough to implement a firewall; you also have to make sure that your firewall complies with the Health Insurance Portability and Accountability Act (HIPAA).
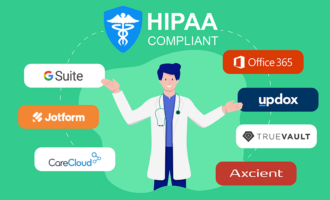
The HIPAA Security Rule stipulates that healthcare providers (i.e., covered entities) must safeguard PHI with policies and technical measures that prevent improper use of this sensitive and confidential information. HIPAA-enabled firewalls can help protect networks and prevent unauthorized access to PHI.
Just so you know
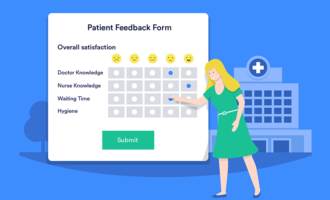
Securely collect patient data, payments, and signatures online with Jotform’s HIPAA-enabled medical forms.
What is a firewall, and what does it do?
Simply put, a firewall is like a digital line of defense that stands between valuable network data, such as PHI, and cyber threats, such as viruses, hacking, and malware. The firewall is a virtual barrier that works according to predefined configurations to block potentially dangerous entities from accessing the data, and to secure the flow of data in and out of the network or computer to ensure it isn’t compromised at any stage.
Firewall controls are configured according to need, enabling various levels of network access to specific individuals. This is an important part of HIPAA compliance, as properly set firewall controls enable that only authorized personnel can access sensitive PHI at the level they need to do their jobs.
Outbound firewall rules that help with HIPAA compliance
There are two kinds of firewalls that medical practices need to be concerned with; the first is outbound firewalls. These firewalls pertain to the kinds of information employees have access to on the internet — the outbound traffic.
For example, most medical practices employ a receptionist who is required to access company email. The firewall controls on the receptionist’s computer allow them to access the company email and other websites necessary to perform their job, but it might be configured to block sites that the job role doesn’t require, like Facebook or Instagram. Allowing access to specific websites is known as whitelisting, and it prevents the employee from visiting websites that aren’t secure and could expose the computer to breaches and malware.
However, doctors or nurses may use their computers for research purposes, and they may not know where they will need to look for information before they begin their search, meaning they need more open access. Practices can blacklist specific sites for these users so that they can go anywhere except to websites known to harbor malicious software or otherwise violate office internet use policies. However, whitelisting is still more effective given the fact that the number of malicious websites is always increasing.
Finally, there will be some computers that don’t need to be connected to the internet. An example is a server that stores electronic medical records (EMR). These computers can be blocked from accessing the internet — eliminating the potential for a data breach — all the while remaining connected to the organization’s network for operational purposes.
Inbound firewall rules that help with HIPAA compliance
When it comes to inbound traffic — allowing connections from the outside — the safest way to enable HIPAA compliance and record safety is to turn off all remote access. However, there may be times a physician or employee has to connect remotely, and it’s critical that the firewall is properly configured.
If remote access is allowed, you’ll need to set up a virtual private network (VPN). A VPN is a private network that acts as an encrypted tunnel for secure data sharing on a public network. Organizations use VPNs to protect sensitive data that’s accessed and shared online. VPN users connect via a unique username and password, as well as a secret code on the specific computer that authorizes its access to the VPN.
The importance of firewall logging
In order to comply with HIPAA, your firewall must be configured to properly log and track all data on your computer systems that interact with patient information.
According to the HIPAA Security Rule 164.312(b), you must have HIPAA audit logs of PHI. These logs provide you with the necessary information to help record any user activity that impacts the firewall. This includes regular activity and activity that might be dangerous or could potentially expose PHI and violate HIPAA or cause a security breach of any kind.
An effective way to handle log management is to evaluate your security strategy and take these steps:
- Decide how and when you’ll generate a log.
- Designate an employee to review the logs on a daily basis.
- Safeguard your stored logs so they aren’t maliciously used by cybercriminals or accidentally altered by employees.
- Have a team and process to review any alerts that appear suspicious.
- Frequently evaluate the log collection process and make any necessary adjustments.
Because most firewalls have limited storage space, practices should use a dedicated server for firewall logging. These logs can be monitored and alert the necessary personnel if unauthorized activity or a possible cyberattack is detected.
The importance of firewalls that help with HIPAA compliance
Firewalls are a crucial component of maintaining HIPAA compliance and securing your practice and all PHI. Make sure that you restrict access to the internet and that you take the time to review the logs for any possible holes. Failure to effectively implement HIPAA firewall controls can put your organization at risk for costly healthcare breaches, HIPAA fines, and the loss of not only patients but also your reputation.



























































































Send Comment:
1 Comment:
August 14, 2020
HELLO WE ARE A LAB THAT NEEDS TO STAY HIPPA COMPLIANT AND KEEP PATIENT FILES AND RESULTS SAFE. WE DONT DO ANY PAYMENTS HERE- CAN YOU PLEASE CALL ME TO GET THIS SET UP? THANK YOU. 678.510.6289